Introduction to Malware Analysis
- Introduction to Malware Analysis
- Preliminary Analysis Techniques
- Environment for Malware Analysis
- Static Malware Analysis
- Dynamic Malware Analysis
- Understanding Malware Behaviour
- Reverse Engineering
- Advanced Static Analysis
- Advanced Dynamic Analysis
- Anti-Reverse Engineering
- Malware Attribution
- Malware Mitigation and Prevention
Malware Attribution
Understanding Attribution Techniques in Malware Analysis
Branch of forensic science.
Attribution in the context of cybersecurity refers to the process of associating a cyber attack or malicious activity with a specific threat actor or group. This process is crucial in understanding the motives, tactics, and potential future actions of the threat actors. This article will explore the various techniques used in malware attribution.
Indicators of Compromise (IoCs)
Indicators of Compromise (IoCs) are pieces of forensic data that cybersecurity professionals use to identify malicious activity on a network or system. IoCs can include IP addresses, URLs, email addresses, file hashes, and specific behaviors that are associated with malware or a cyber attack.
By collecting and analyzing IoCs, cybersecurity professionals can identify patterns and links that can lead to the attribution of a cyber attack to a specific threat actor or group.
Digital Forensics
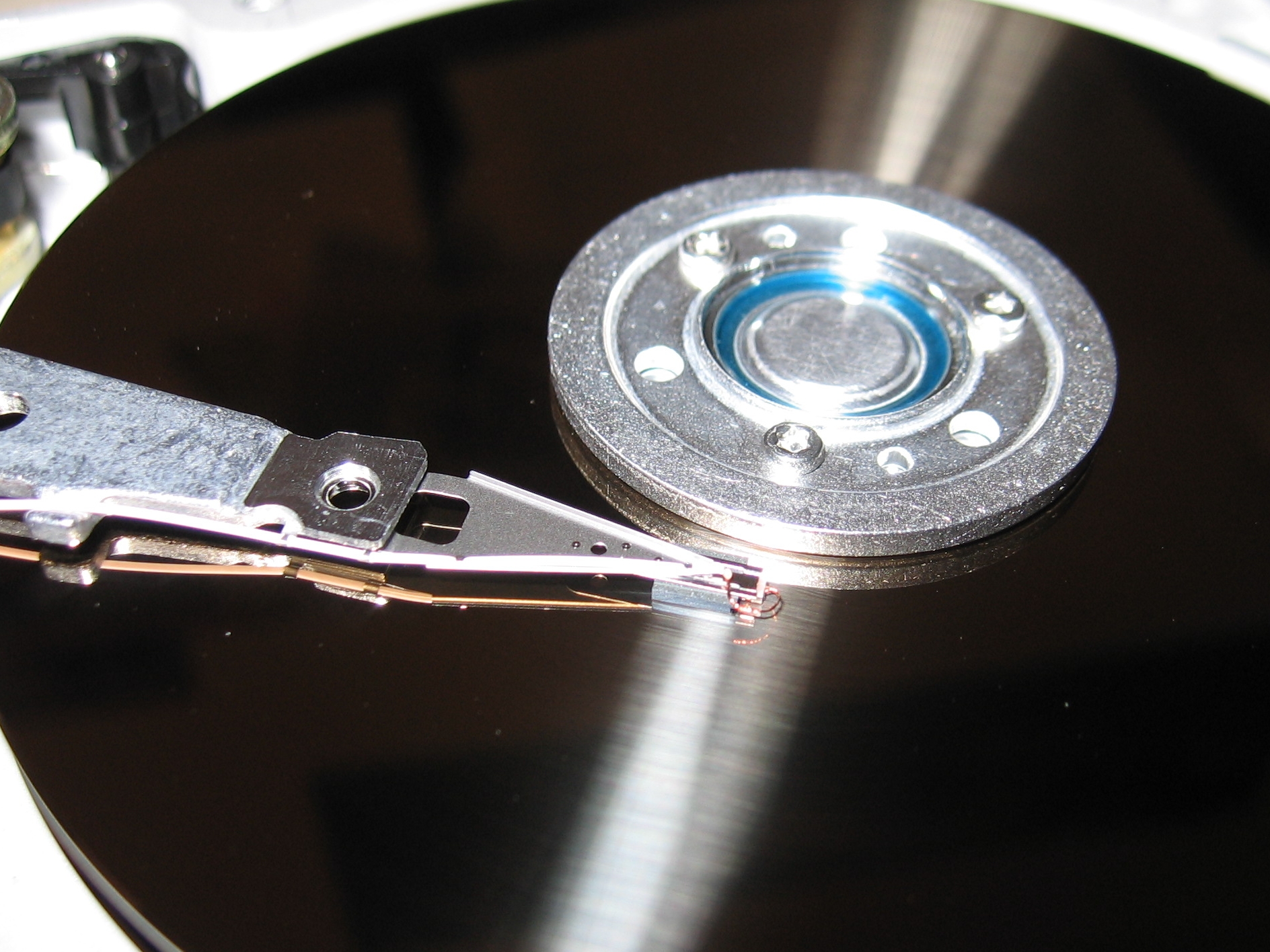
Digital forensics plays a crucial role in malware attribution. It involves the collection, preservation, analysis, and presentation of evidence from digital sources. This evidence can include log files, hard drives, emails, and other digital artifacts.
Digital forensics can provide valuable insights into the methods and tools used by threat actors, which can help in attributing a cyber attack. For example, the analysis of a malware's code can reveal specific coding styles or techniques that are unique to a particular threat actor.
Open Source Intelligence (OSINT)
Open Source Intelligence (OSINT) refers to the collection and analysis of publicly available information. This can include information from news articles, blogs, social media, and other public sources.
OSINT can provide valuable context and background information that can aid in malware attribution. For example, a threat actor may have previously claimed responsibility for similar attacks on a social media platform, or a news article may report on a specific threat actor's tactics and targets.
Challenges in Attribution
While the techniques mentioned above can provide valuable insights, attributing a cyber attack to a specific threat actor or group is not always straightforward. There are several challenges in attribution, including:
- False Flags: Threat actors often use techniques to mislead investigators and make it appear as if another group or country is responsible for the attack.
- Shared Tools and Techniques: Many threat actors use the same tools and techniques, making it difficult to attribute an attack based on these factors alone.
- Lack of Direct Evidence: In many cases, there may not be direct evidence linking a threat actor to a specific attack, making attribution based on circumstantial evidence.
Despite these challenges, the techniques discussed in this article, when used in combination, can provide valuable insights and lead to more accurate attribution of cyber attacks.